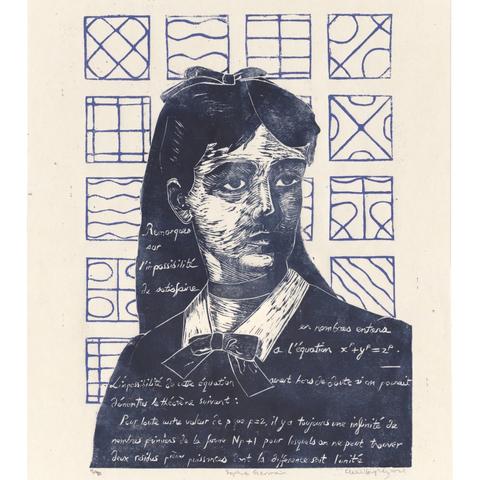
Happy birthday to French mathematician, physicist and philosopher Marie-Sophie Germain (1776 – 1831), known as Sophie. She taught herself mathematics using books in her father’s library and by corresponding with leading mathematicians of her day, including Lagrange, Legendre and Gauss, initially using the pseudonym Monsieur LeBlanc. 1/n
#linocut #printmaking #sciart #mathart #SophieGermain #ChladniFigures #mathematician #Fermat #womenInSTEM #physicist
#mathematician
An Incredibly #Ingenious Way to Make #Crops More #Resistant Against #Diseases: Medium
How #ClimateChange could make #Earth's #SpaceJunk problem even worse : Space
Was #SamAltman Right About the #Job Market? : Misc
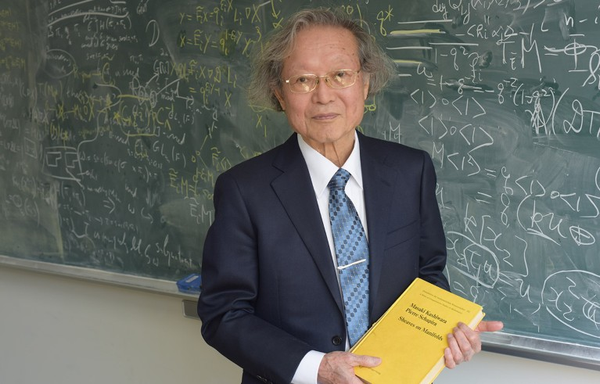
#Mathematician who reshaped #Theory of #Symmetry wins #AbelPrize : Nature
Check our latest #KnowledgeLinks
I have a question for the #Astrophotographer and #Mathematician folks out there.
What is the smallest number of frames you could perform a drizzle transform on?
Could you, for example, perform it on two frames, and then submit that image to a livestacking process?
Does this idea even make sense?
As for "Why do this?", I am looking at the #SmartTelescope world, and wondering if you could perform the resolution increase in conjunction with live stacking, without resorting to post-processing. This is to attempt to allow a software-only capability upgrade, while still maintaining the convenience.
I figured I'd ask here first, because (conceptually) it seems almost too simple.
#astronomy #Astrodon #DumbQuestion
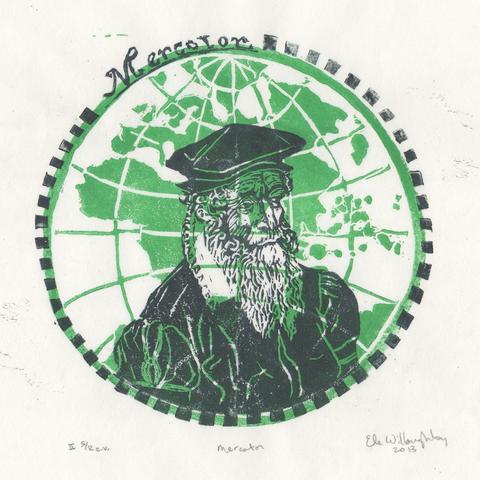
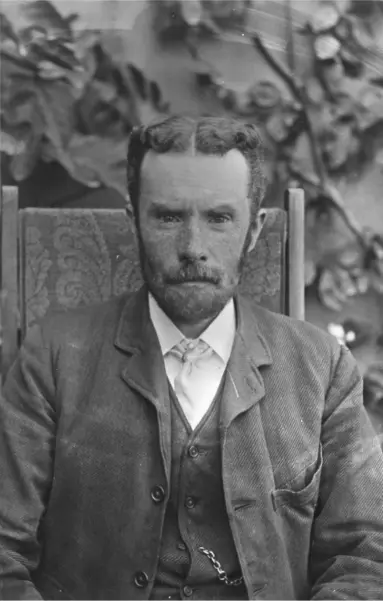
Happy birthday to Gerardus Mercator (1512-1594) renown Flemish cartographer.
What made Mercator a great #cartographer, was in fact his abilities as a #mathematician -and like those of us scientists who feel compelled also to create art he was wasn’t hindered by his immense ability as an engraver. He produced beautiful world maps (a version of which is depicted in this print), globes, 1/n
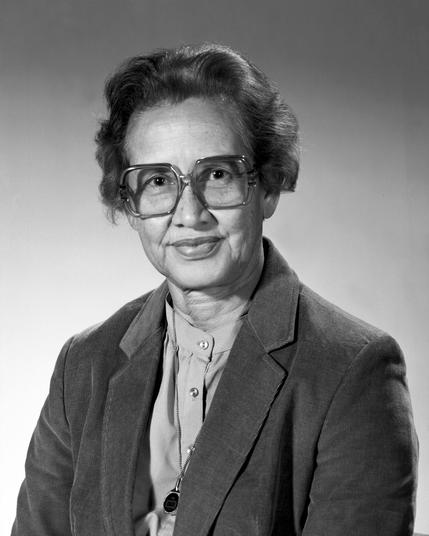
#OnThisDay in 2020, #KatherineJohnson, American NASA #mathematician (portrayed in film Hidden Figures), died at 101.
#RIP
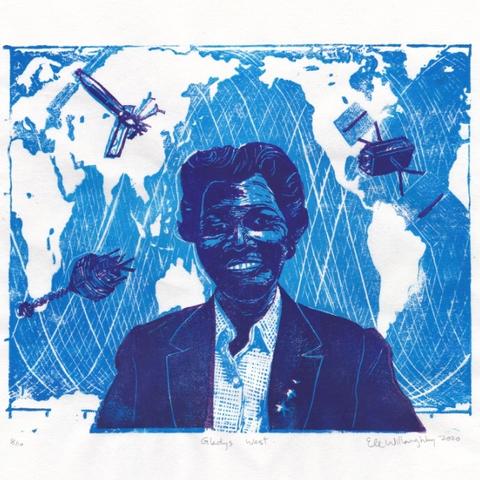
For #BlackHistoryMonth: #mathematician & geodesist Gladys West (née Brown 1930)! Shown with satellite tracks & 3 satellites important to her career: Seasat, GEOS-3 & a GPS satellite. Her work, using math to precisely model the shape of Earth, laid the groundwork for GPS! Born to sharecropper parents in Virginia, she graduated with a Math BSc in ‘52 then MSc at VSU in ‘55. 1/n
Happy birthday to Marjorie Rice (née Jeuck, 1923–2017) who discovered 4 new pentagonal tilings of the Euclidian plane!
The San Diego mother of 5 (6th died in infancy) completed half a correspondence art course after high school & had no training as a #mathematician but was always interested in #math & art. She began to follow SciAm writer/amateur mathematician Martin Gardner’s column, rushing to devour the magazine before her
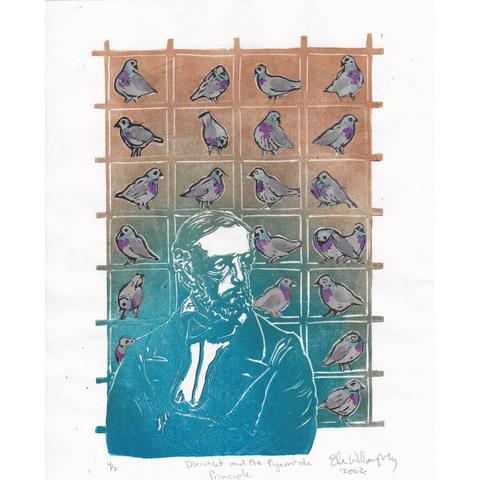
Happy birthday to #mathematician Johann Peter Gustav Lejeune Dirichlet (1805 –1859)! My lino block print illustrates the famous mathematical tool known as the pigeonhole principle, which states that if n items are put into m containers, with n > m, then at least one container must contain more than one item. You can imagine a bunch, call it m, pigeonholes and n pigeons, where n > m; to fit the pigeons in the pigeonholes,
#OnThisDay Birth Anniversary of #English #Writer Charles Dickens (1812) - regarded by many as the greatest #Novelist of the Victorian era.
Birth Anniversary of #English #Mathematician G. H. Hardy (1877) - mentor of the Indian mathematician Srinivasa Ramanujan.
Happy Birthday Tawakkol Karman (1979) - co-recipient of the 2011 Nobel Peace Prize, becoming the first Yemeni, the first Arab woman to win a #NobelPrize.
TIL about Oliver Heaviside.
He was an #electrician , #mathematician and #physicist who made major contributions to the field of electro-magnetism.
He was born in #Camden , in #London . He discovered ways to improve the performance of telegraph lines (the internet of the late 1800s), he patented the coaxial cable, and he re-formulated the #Maxwell equations on electro-magnetism into the form they have today.
He was a Fellow of the Royal Society, and was the first recipient of the Faraday Medal.
He died after falling off a ladder.
https://en.wikipedia.org/wiki/Oliver_Heaviside
https://www.english-heritage.org.uk/visit/blue-plaques/oliver-heaviside/
#TIL #TodayILearned
It’s #BlackHistoryMonth so it’s a good time to celebrate the extraordinary mathematician and NASA scientist Katherine Johnson (née Coleman; August 26, 1918 – February 24, 2020). One of the first Black women employed as a NASA scientist (and its predecessor NACA), she was known for her mastery of complex manual calculations of orbital mechanics and played a pivotal role in the success of
#HelenaRasiowa (20 June 1917 – 9 August 1994) was a Polish #mathematician. She worked in the #foundationsOfMathematics and #algebraicLogic.
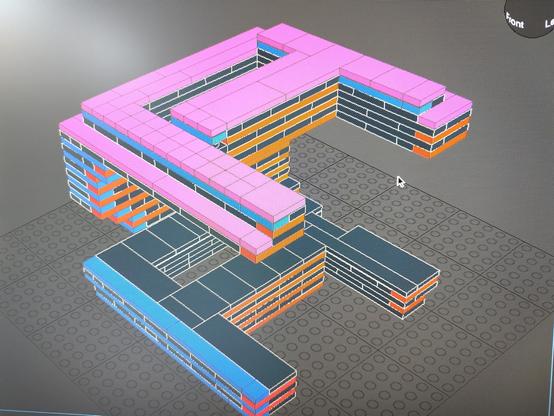
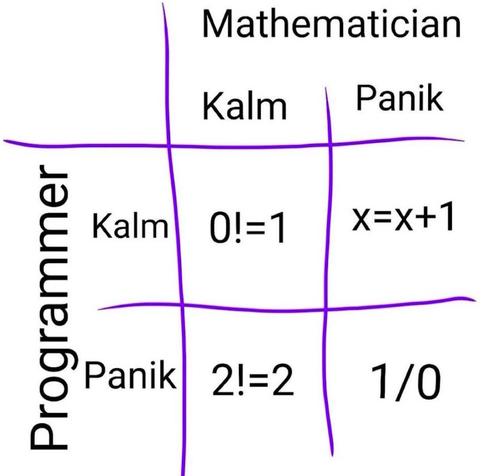
I'm busy writing a #Python program that creates (virtual) #Lego #moc files for #LEOCad. But, I've hit a #combinatorics wall, and my #maths-fu fails me here...
Are/is there any #programmer and/or #mathematician who can help me?
See picture for what I'm trying to do...
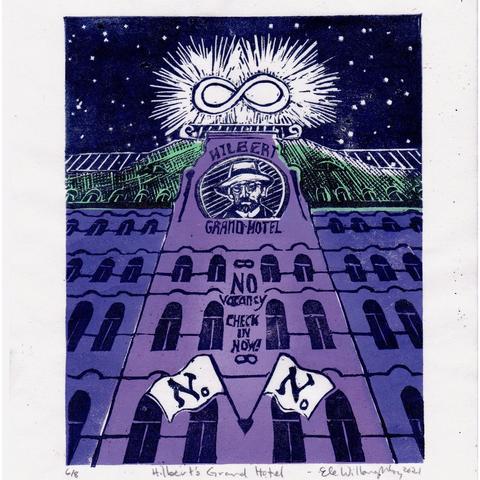
Happy birthday to #mathematician David Hilbert (1862-1943)! This #linocut illustrates the paradox of Hilbert’s Grand Hotel, a thought experiment conceived by Hilbert in 1924 to show the paradox of infinite sets. If you imagine a regular hotel with a finite number of rooms, if they are all filled you can’t add more guests. In an imaginary infinite hotel however, guests are always welcome!
#OnThisDay Birth Anniversary of #Economist W. Arthur Lewis (1915) - famous for his contributions to development economics. He won the Nobel Memorial Prize in Economic Sciences in 1979.
Birth Anniversary of #Mathematician David Hilbert (1862) - known as one of the founders of proof theory and mathematical logic.
@djb (Daniel J. Bernstein) tooted about a new blog post[1] he published. It's here:
https://blog.cr.yp.to/20250118-flight.html
It's interesting. He's a #mathematician and software guy that in more recent years has been known mostly for his work in #cryptography, #theoretical and #practical. You're probably using his #Curve25519 every day in your #communications.
I'm not a mathematician (by a long shot), but it's written in a pretty accessible manner - it's not #formulae and #turgid academic #prose.
The central point he's getting at, by my possibly-mistaken understanding of it, is that current "common sense" about when attacks against pre-quantum cryptography like #RSA (and therefore when post-quantum cryptography becomes critical) are badly mistaken - based on bad assumptions about how attacks work, how they're implemented, and on badly #extrapolating from those bad assumptions using logic that doesn't actually represent the way attacks are developed and become practical.
TL;DR is something along the lines of "#quantum cryptographic attacks against RSA will be practical sooner than most people think, and you should be deploying quantum-resistant cryptography now, not later".
It's worth reading if you're at all interested in #crypto and #security stuff.
He also mentions a project he's involved in that has been discussed separately, transparent post-quantum tunnelling for unmodified #server and #client #software. Link in post.
[1] Written more like a conference presentation, FWIW.
Happy birthday to Russian #mathematician & writer Sofia Vasilyevna Kovalevski (1850-1891). Her contributions to analysis, differential equations & mechanics include Cauchy-Kovalevski theorem & the famed Kovalevski top. She was 1st woman appointed to full prof in N Europe or to serve as editor of a major sci journal. She is also remembered for her contributions to Russian literature. All of this despite living when women were still barred from attending
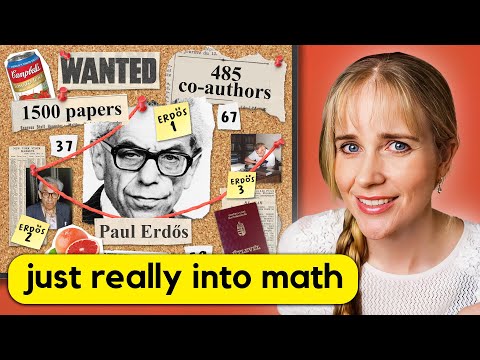
The Mathematician So Strange the FBI Thought He Was a Spy
#math #mathematic #mathematician
https://www.youtube.com/watch?v=hZQqfy5A1k4&list=UULF52kszkc08-acFOuogFl5jw&index=1
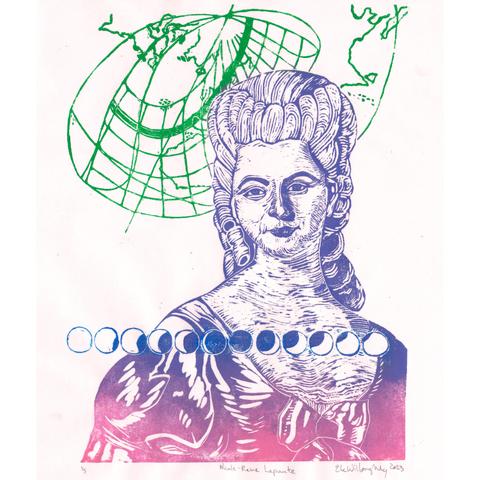
Happy birthday to #mathematician & #astronomer Nicole-Reine Lepaute (1723-1788)! My #linocut celebrates her calculated path of the solar eclipse of 1764. She also worked with Alexis Clairaut & Jérôme Lalande to precisely calculate the date of return of Halley’s Comet solving the notorious 3-body by hand (including the gravitational pull of Jupiter & Saturn on orbit). They worked in parallel, calculating for 6 months straight barely stopping